Network Infrastructure

Isolated Castles: Incident Response in the New Work From Home Economy
Since the shift to work from home, there's been a paradigm shift in the IT and security industry. The...
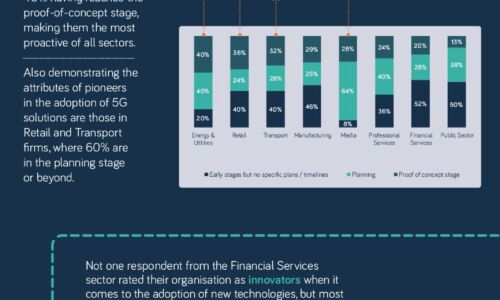
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...
Report: ICS/OT Cybersecurity 2021 Year in Review
Dragos is excited to present the fifth year of the annual Dragos Year In Review report on Industrial...

How SASE empowers your business for the cloud generation.
Wide area networks (WANs) have played a critical role in business growth for several decades. Early WANs...

5G for the enterprise
With a desire to better understand the current, on-the-ground reality for enterprises and organisations...
DDoS attack trends for Q2 2021
Cloudflare's network protects approximately 25 million Internet properties, giving us deep insight into...

Cloud networks: Shifting into Hyperdrive
Public cloud is driving digital innovation. As IT organizations around the world continue to radically...

GigaOm Radar for DDoS Protection
Cloudflare ranked higher than any other assessed vendor and is named a 'Leader' and 'Fast-mover'' in...
Securing financial services network data
Financial services is one of the most tightly regulated business sectors. The FSA, the Data Protection...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




