Network Infrastructure
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

Case Study – JUSTWork
JUSTWork wants to invigorate the concept of the workplace. For that to be possible, JUSTWork needs an...

Understanding Log Analytics at Scale
The humble machine log has been with us for many technology generations. The data that makes up these...

Connected cities and places
Improving digital infrastructure is key to enabling a smarter city or place to develop, thereby creating...

Guide to Transform Your Network with Advanced Load Balancing
To evolve with the times and deliver capacity to the business, network ops teams are transforming the...

5G in the Transport sector
The Transport sector is pioneering the adoption of 5G connectivity, and yet it's doing so with quiet...

Struggling To Securely Keep Up With Digital Acceleration
In today's digital economy, businesses must move fast, rapidly adapting to changes. Increasingly, this...

IDC Whitepaper: Achieving Network Modernization for the Decade Ahead
Every organization is now defined by the digital services it delivers. From engaging customers with new...
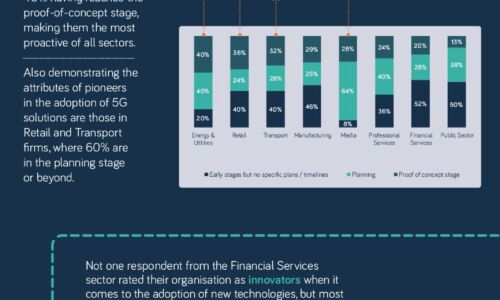
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...

Aruba Unified Infrastructure
Network infrastructure and operations teams have never been more stretched. Hyper-distributed edge environments...

Protecting Your Hybrid and Hyperscale Data Centers
Organizations are building hybrid data centers that consist of composable and scalable architectures....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


