Software

What Separates the Best from the Rest
Some IT organizations have the speed and adaptability to change course quickly when disaster strikes...
A Business Case for Customer Data Management
If you're reading this, you've already arrived at a couple of realizations: This guide will help you...
An Insider’s Look at Enterprise Cloud Adoption
It's a well-known fact that more businesses are adopting cloud computing technologies, and the overall...

Security Considerations in Industrial 5G Environments
The convergence of market demand and new digital capabilities is helping companies transform their operations....

A Guide to API Security
Gartner was right when they asserted that by 2022, API abuses will 'move from an infrequent to the most-frequent...

Hybrid Cloud: A Smart Choice For AI And HPC
High-performance computing (HPC), once the purview of academia, is going mainstream. Often used to train...

Lessons from past vulnerability exploits and how WAF can help
Fight web attacks in seconds without slowing down your website. The onset of 2020 was marked by the disclosure...

Data-Empowered Construction
In today's construction industry, data analytics is essential for maximizing performance and staying...
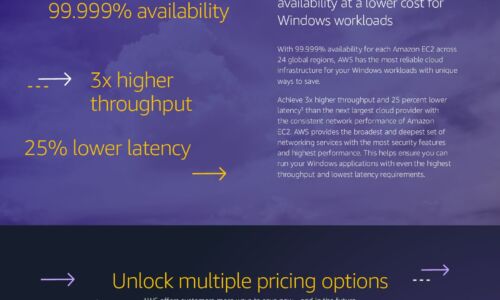
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




