Software
Businesses that make big moves are seeing big opportunities
New opportunities have arisen for finance leaders—but only if you're willing to make big moves in unpredictable...
Workforce Management in Multiservice Organisations
How to create a more effective approach in the service and facilities management industries. Siloed operations...
The Modern Mailer
The world of print and postal communications is changing. With reducing average run lengths and the ongoing...

Aruba ESP (Edge Services Platform) - Harnessing the Power of the Edge
Every decade or so, we've seen the technology market undergo major shifts. Over the past few decades,...
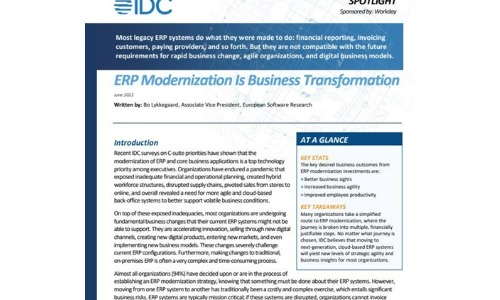
ERP Modernisation Is Business Transformation
Build agility and get the most from your ERP modernisation. Many organisations approach ERP modernisation...

The Road To Digital Experience Success
The world of work is not changing. It has already changed. Firms that have not boarded the ship need...

SASE-Ready WAN Edge for the Work from Anywhere Era
Enterprise networks are on the verge of a major tipping point, driven by the shift from employees working...
The Hidden Cost of Free M365 Security Features
All email, cloud, and compliance solutions are not created equal. As organisations make the move to Microsoft...

Ransomware Survival Guide
Be Ready for Ransomware Ransomware is an old threat that just won't go away. While overall volumes have...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




