Mobile Computing

5 Signs You Need To Upgrade Your Phone System
If you are like most people, the sudden rush to send workers to work remotely highlighted some limitations...

The Road to Recovery - Growing Your Business in China
The pandemic is fast tracking the digital transformation of organisations in China (and the region) as...

CISSP For Dummies
Secure your CISSP certification! If you're a security professional seeking your CISSP certification,...
DEIB Analytics: A Guide to Why & How to Get Started
Gain insights from RedThread Research on why businesses are focused on diversity, equity, inclusion and...

Two-Factor Authentication Evaluation Guide
In this guide, you will learn how to evaluate a solution based on: ...
4 tips to ensure your board is ready for a successful AGM
The 2022 AGM season is on course to see unprecedented levels of challenge for boards and businesses....

What Separates the Best from the Rest
Some IT organizations have the speed and adaptability to change course quickly when disaster strikes...

Insurance MFA case study – on-premise and multiple integrations
UNIQA Czech Republic is part of one of the leading insurance groups, UNIQA, located in Austria, Central...

5 signs your SaaS company needs to improve its usage data management
If your SaaS company offers usage-based pricing, there's a good chance you've built an in-house solution...
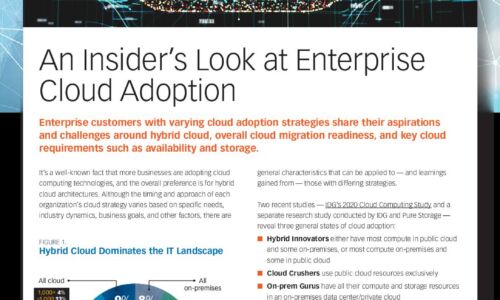
An Insider’s Look at Enterprise Cloud Adoption
It's a well-known fact that more businesses are adopting cloud computing technologies, and the overall...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


