Data Center

You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...

Dell ProSupport Plus vs. HP and Lenovo
While resolving a hardware issue on an employee's laptop normally take time and can disrupt the normal...

Security and risk management in the wake of the Log4j vulnerability
Security leaders agree: Log4j has irrevocably changed the risk landscape. Get a quick refresher on the...

Seven Strategies to Securely Enable Remote Workers
Is your organisation ready to securely support a wide range of remote workers in the wake of a global...
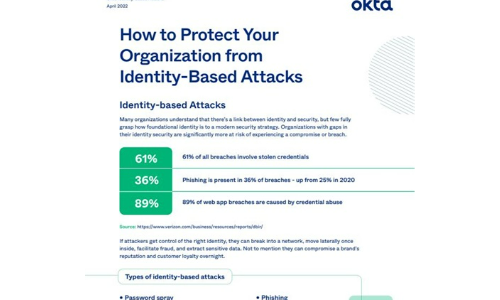
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Redefining Healthcare in the Cloud
Helping you visualise clinical healthcare innovation, and the future of personalised experiences in the...

10 Signs It’s Time To Review Your Endpoint Protection
Cyber attacks are increasing in frequency, sophistication, and effectiveness. The ongoing trend of successful...

Edge Computing in Telco Networks: Gaining the Competitive Edge
Earlier this year, Wind River® teamed up with F5, Schneider Electric, and Heavy Reading on a global...

The Anatomy of Account Takeover Attacks
Bad bots are on every website with a login page. Even yours. Hackers and fraudsters use bots to validate...

Lessons from REvil's Return
Ransomware is not just another buzzword. It is a very real threat to businesses and educational institutions...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



