IT Management

Networking and Information Systems (NIS) Directive
The NIS Directive has been designed to work alongside data protection legislation. It will be governed...
8 Ways To Evaluate An MDR Provider
For many organizations, digital transformation had been a business initiative for years, but the pandemic...

Unleash the Power of Supplier Data
Today, most big companies have a foggy, disjointed picture of their suppliers. Why? Because their supplier...

Accelerate and Secure Your SQL Server DevOps CI/CD Pipelines
If you want your SQL Server database development to catch up with agile application development, you'll...
Complete Cloud Security for Legal Firms
Thales have a long history in securing some of the world's most sensitive data, and law firms are increasingly...

What you need to know about upcoming ESG regulations
New ESG regulations are being proposed across the world. But ESG is about more than just meeting requirements....

The Forrester Wave™: Privileged Identity Management
in our 35-criterion evaluation of privileged identity management (PiM) providers, we identified the 11...
How financial firms build stellar experiences in the cloud
From ordering takeout on an app to joining video calls, the way your customers work and play is constantly...
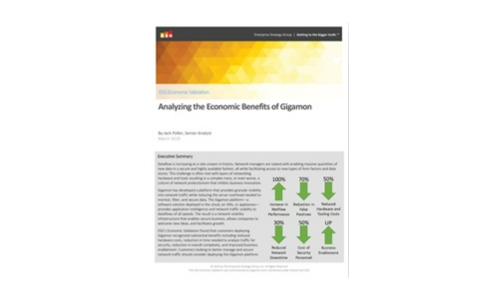
Analyzing the Economic Benefits of Gigamon
This ESG Economic Validation is focused on the changes companies can expect when deploying Gigamon's...
Join POV with KPMG - Future ready insurance leaders
Risk is at the heart of the insurance business. While disasters and disruption can lead to massive payouts,...

Spotlight: The State of the UK and Ireland Mid-Sized Business and IT
Medium-sized businesses are central to our economies, but this varied market is hard to analyse. So,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


