Become (and remain) the disruptor
If you thought digital disruption was a one-off process to be completed (or resisted), unlocking a new,...
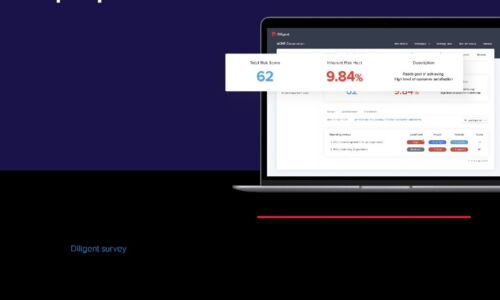
A Buyer's Guide to Audit Management Software
For today's internal audit teams, the audits themselves are only one part of a growing scope of responsibilities. Executives...
Effective CISO Presentations to the Board: Top Tips & Checklist
As a CISO, you have crucial info to convey about cyber risk, and your board wants to hear it. In a recent...

Hybrid Work Drives the Need for ZTNA 2.0
The COVID-19 pandemic has had a profound effect on the world. Businesses have compressed into months...
2021 Technology Industry Cyber Threat Landscape Report
The technology industry is a top target for both cybercriminals and state-sponsored cyber espionage groups....

Three Top Trends in Higher Ed IT for 2021 and Beyond
We've had a tough 2020, but the ability to work and learn online from anywhere has been popular with...

Digital Document Processes In 2020: A Spotlight On E-Signature
The COVID-19 pandemic has transformed how and where we work. Businesses have had to respond quickly to...

The Best of Both Worlds: Hybrid IAM Offers Flexibility and Enhanced Security
One of the fastest growing segments of the Identity and Access Management (IAM) market is the cloud segment. Increasingly,...

CIO Essential Guidance: Intrinsic Security
Despite massive spend to protect enterprise digital assets, security breaches are still on the rise....
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Defending Ukraine: Early Lessons from the Cyber War
The latest findings in our ongoing threat intelligence efforts in the war between Russia and Ukraine,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.