
Expose the Uncertainty: Best practice for reporting risk
With cyber threats increasing, it's vital for business leaders to understand and mitigate risks that...
Chatbot Starter's Guide
Is your contact center struggling to determine which chatbot solution is right for you? This eBook can...

Digital Document Processes In 2020: A Spotlight On E-Signature
The COVID-19 pandemic has transformed how and where we work. Businesses have had to respond quickly to...

The New Future of Work
To address the challenges of 2020 and emerge stronger in this New Future of Work organisations need to...

Cloud Security Challenges
The need for speed and agility in today's always-on, always-connected digital business has led IT teams...

IDC white paper security
The business criticality and cyber-risk of endpoint devices could not be greater. With the COVID-19 pandemic,...

Guidelines for an Effective Cybersecurity Incident Response Plan
Organizations with a cybersecurity incident response plan experience a lower average cost (by $2.46M)...
How to achieve a 3x ROI with Slack
Our new remote reality makes collaboration tools more important than ever before. These tools define...
Common Browser Isolation challenges, and how to overcome them
A growing number of security teams are implementing a Zero Trust security strategy, in which no application,...
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...

How to Build a Micro-Segmentation Strategy
Micro-segmentation reduces your attack surface and prevents the spread of breaches inside your data center...

One secure platform for banking and capital markets
Easy, secure client experiences are the new gold standard in financial services. Whether you're talking...
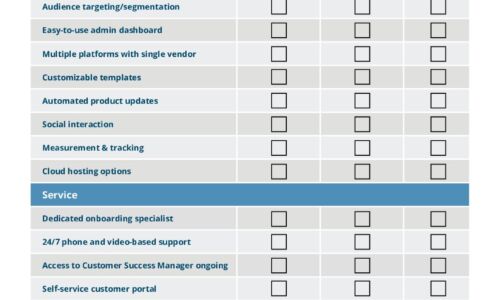
How to chose a managed extended detection and response solution
Managed Detection and Response (MDR) solutions are specialized security services that allow an organization...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
