MandA IT Integration Checklist: Active Directory
If your organization is involved in a merger and acquisition, the impending IT integration project might...
Top Threat Detections Seen Across Healthcare Organizations
We consider the relationship between Healthcare and Cybersecurity today. How can healthcare security...

8x8: Collaboration and AI Take Customer Care to the Next Level
This buyers guide examines the North American contact center market for both premise- and cloud-based...

Report: Forrester TEI for CSM
To deliver effortless, end-to-end customer experience every time, all parts of your organisation need...
Four Compliance Trends For 2021
If 2020 was the year the financial services industry was turned on its head, what's in store for compliance...
2022 MSP Threat Report
This report was created by the ConnectWise Cyber Research Unit (CRU)—a dedicated team of ConnectWise...
Aberdeen Research: How IT Leaders Modernize Operations with E-signatures
In this knowledge brief, we'll analyse how organisations today are modernising sales practices and operations...

Case Study - Malwarebytes Endpoint Protection and Response
Malwarebytes cut potential downtime to a matter of hours rather than weeks. Malwarebytes complements...

Meaningful Metrics for Human Cyber Risk
By focusing on meaningful security metrics, organizations can benchmark, assess progress, and measure...

Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
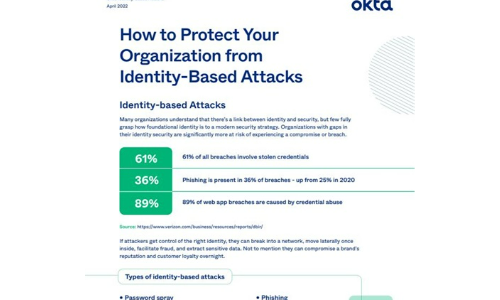
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.