Disaster Recovery
Unlock the Power of Hybrid Cloud with Consistent Operations eBook
Embracing a hybrid cloud operating model creates new possibilities for IT organizations, paving the way...
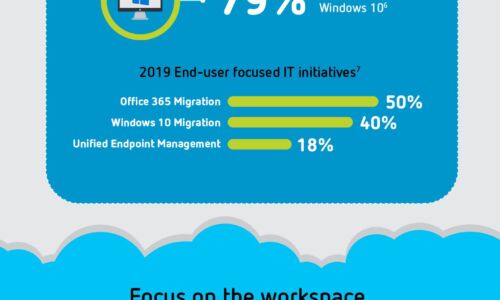
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

How Malware Can Steal Your Data
As applications drive business, more and more valuable data is accessed and exchanged through them. Cybercriminals...

Case Study - Malwarebytes Endpoint Protection and Response
Malwarebytes cut potential downtime to a matter of hours rather than weeks. Malwarebytes complements...

State of Ransomware Readiness Report
2021 has been the year of ransomware. Overall, 80% of businesses around the world have been attacked...
Essential Operational Resilience
COVID-19's far-reaching impacts have thrashed many companies' Plan-A strategies, yet the pandemic offers...

VMware Cloud Workload Migration Tools
Before starting a cloud migration project, it is critical to understand the strategies and tools available...

Building A Better Cloud Begins With Better Infrastructure
The modern enterprise lives in a multi-cloud world, where delivery of infrastructure resources and IT...

Windows Server 2019 and PowerShell All-in-One For Dummies
Windows Server 2019 and PowerShell All-in-One For Dummies offers a single reference to help you build...

Three Ways to Make Cloud Your Business
The role of IT infrastructure and operations leaders has dramatically changed, and cloud evolution continues...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.