Backhaul

3 Secrets to SD-WAN Success
Organizations are turning to software-defined wide area networks (SD-WAN) to intelligently route traffic...

Beyond on-demand for DDoS defense
The global pandemic changed the way we work, travel, play, and stay connected — increasing our reliance...

Secure Access Service Edge (SASE): 7 Ways Your Business Benefits
The benefits that SASE offers organizations helps explain why Gartner estimates that by 2025, 80% of...

Multi-cloud Load Balancing for Dummies
Legacy hardware-based load balancers don't meet modern enterprise application delivery requirements in...

Hybrid Work Drives the Need for ZTNA 2.0
The COVID-19 pandemic has had a profound effect on the world. Businesses have compressed into months...

How SASE empowers your business for the cloud generation.
Wide area networks (WANs) have played a critical role in business growth for several decades. Early WANs...

Cloud networks: Shifting into Hyperdrive
Public cloud is driving digital innovation. As IT organizations around the world continue to radically...

5G in the Transport sector
The Transport sector is pioneering the adoption of 5G connectivity, and yet it's doing so with quiet...
WAN-as-a-Service enables networks to respond to evolving IT needs
Traditional methods of building wide area networks (WANs) have always had limitations, but fell even...
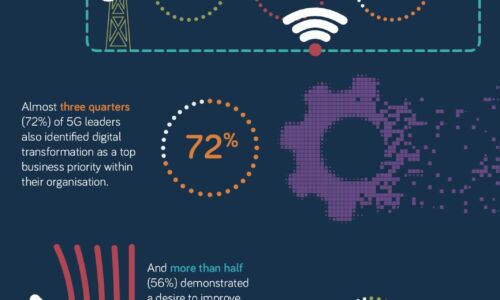
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

Implementing the NIST Zero Trust Architecture with Zscaler
The National Institute of Standards and Technology (NIST) has defined the core components of zero trust...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.