Latest Whitepapers

Learn How to Build Resilient Global Applications
Quick 5 minute read! Deliver high performance and always-on applications anywhere with Active-Active. Today's...

3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...
The Book of Knowledge -Customer Experience
Every customer interaction matters. But how can you deliver effortless experiences that build long-term...
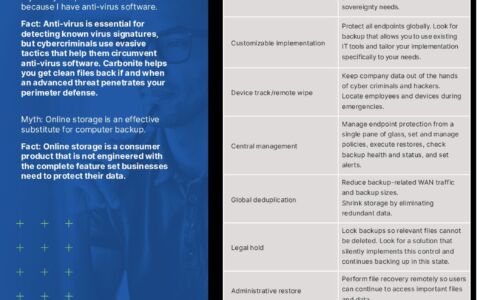
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

The State of Application Security in 2021
Barracuda commissioned independent market researcher Vanson Bourne to conduct a global survey of 750...
3 benefits of Citrix ADC with flexible licensing
You need flexible application delivery controller solutions that streamline your move to the cloud. See...
The Passwordless Future Report
Every company has to become a technology company in order to survive and thrive in today's competitive...

Dell EMC PowerStore: Data-centric, Intelligent, Adaptable Storage
This report provides a brief introduction to Dell EMC's PowerStore mid-range storage appliance and documents...
Complete Cloud Security for Professional Services
Thales have a long history in securing some of the world's most sensitive data, and professional service...

Ponemon Report
Ponemon surveyed 1,826 IT professionals globally to understand the state of SD-WAN, SASE and Zero Trust...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.