Latest Whitepapers
CIO Perspectives Magazine issue 7
Business continuity for CIOs, explained. Legacy systems weren't built for the pace of change that CIOs...
A Five-Step Plan to Move Your Apps to the Cloud
Cloud applications, platforms, and services are changing the way enterprises compete for customers. The...
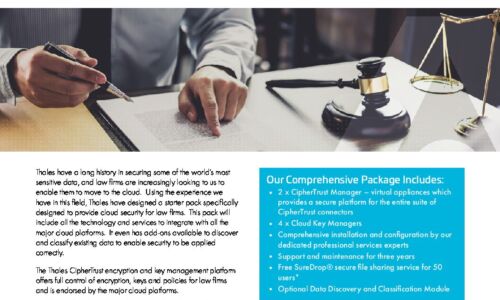
Complete Cloud Security for Legal Firms
Thales have a long history in securing some of the world's most sensitive data, and law firms are increasingly...
Enterprise Cloud Solutions
Many traditional infrastructure vendors would have you believe that hyperconverged infrastructure is...

The Impact of Moving to Independent, Third-Party Software Support
When organizations consider the amount of their IT budget that is spent on yearly maintenance, many focus...
Why dirty data can stop quote-to-cash processes in their tracks
It's been 15 years since mathematician Clive Humby uttered those famous words: 'Data is the new oil....

HP Proactive Insights Experience Management
Today's work environment looks a lot different than it used to. And it's still evolving. More of us are...
Leadership trends report: technology excellence
There was a time when the IT organization's role was clear and well defined. Spec out the workstations,...
How Virtual Desktop Infrastructure Enables Digital Transformation
Virtual desktop infrastructure (VDI) is a foundational technology that many organizations leverage as...
Intelligent Authentication and Fraud Prevention Intelliview
In this third annual Intelliview, Opus Research and SymNex Consulting provide enterprise decision-makers...

13 Email Threat Types to Know About Right Now
A cyberattack can affect your business in many ways, depending on its nature, scope, and severity. In...

The Benefits of the Cloud: A Guide for IT Leaders
Increase your organization's resiliency and agility. Working with agility and driving innovation can...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.