Storage

The AI & Machine Learning Imperative
Companies across various industries are seeking to integrate AI & machine learning (ML) into workflows...

The Essential Guide To Machine Data
Machine data is one of the most underused and undervalued assets of any organization, yet it contains...

How to Meet Digital Expectations in IT: A European Study
More than 4,000 customers have told they us they want to go digital, while 800 senior decision makers...
AWS for Healthcare: Accelerating the Future of Personalized Healthcare
For healthcare organizations, the challenge of providing patient centered care amid ever-increasing costs...

Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...
AI-powered contact centers to improve customer experience
Leverage AWS Language AI services to enhance customer experiences It's time to leave behind the challenges...

The Gorilla Guide to Achieving IT Asset Management Success
ITAM is about knowing what you've got, where it is, who's using it and how much it costs. If you want...

The Challenge of Migrating Higher Education Applications to the Cloud
Explore the challenges the higher education sector faces when it comes to migrating applications to the...
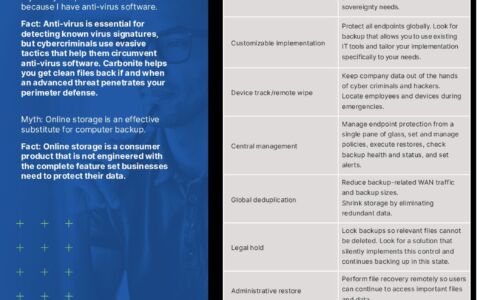
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

Transform Your Field Service with a Great Customer Experience
Full Offline Working, Flexible Architecture, Reusable Components Faced with pressures from both the business...

Intelligent technology for media workflows
Technology in media evolves quickly. Once seen as buzzwords, AI and machine learning (ML) are now crucial...

Securing Digital Innovation Demands Zero-trust Access
To accelerate business and remain competitive, CIOs are rapidly adopting digital innovation initiatives...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

