Storage
How Intrinsic Security Protects Against Business Disruption
When it comes to IT, disruption is just another day at the office. From fending off cyberattacks to incorporating...
Refine your data strategy
Get more out of data and machine learning. Data, analytics, and machine learning have the potential to...
5 Myths about Privileged Access Security for AWS
In today's modern enterprise, more companies rely on an IaaS model. In fact, 93% of IT decision makers...

How Cloudflare Bot Management Works
Cloudflare Bot Management applies automated, data-driven approaches to managing bots. By applying machine...

Networking All-in-One for Dummies
Becoming a master of networking has never been easier Whether you're in charge of a small network or...
Everything You Need to Know About Electronic Signature
Stacks of papers that need to be signed, filing cabinets full of paperwork— these are quickly becoming...

Dell Technologies Continuously Modern Storage Whitepaper
Modernize Data storage to Accelerate Operations and Digital Business Initiatives. Learn more about Dell...

The UK 2020 Databerg Report Revisited Executive Summary
Cloud technology hasn't been around for long, but it's evolution in that time has been nothing less than...
The US Customer Experience Decision-Makers’ Guide 2019-20
The US Customer Experience Decision-Makers' Guide is a major annual report studying the CX strategy,...
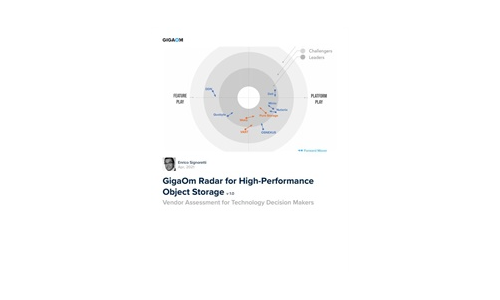
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....

Solve your call center’s seasonal capacity problem
Seasonal surges in capacity, while difficult, are par for the course for most businesses. And while there's...

The Enterprise Guide to Migrating to the Cloud
Enterprises worldwide are competing to develop the most innovative and reliable applications to meet...

3 Ways Emotional Connections Can Power CX
When personalization isn't paying off and data doesn't help you make sound decisions, it's time to renew...

Enterprise Backup and Recovery Made Easy
Protecting enterprise data in a complex IT environment is challenging, time-consuming, cumbersome and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.