Server

Tintri Introduces SQL Integrated Storage
What is SQL Integrated Storage? A SQL database is, essentially, a collection of files with associated...

OWASP Top 10
The nonprofit Open Web Application Security Project (OWASP) works to improve the security of software,...

You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...

Demystifying Zero Trust
Enter zero trust, a cybersecurity philosophy on how to think about security and how to do security. Zero...
SASE: The Network Of The Future Is Here Today
Your business can no longer rely on the old hub-and-spoke network model with its long hauls back to the...
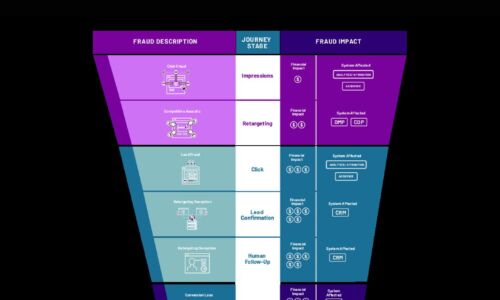
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

8 Deployment Pattern Structures to Transform your CI/CD
Modernize your DevOps with the right deployment pattern Good deployment patterns mean fast and repeatable...

Next Gen Infra Accelerate Innovation with AWS
Run any application in the cloud, on premises, and at the edge More businesses are discovering the power...
Common Browser Isolation challenges, and how to overcome them
A growing number of security teams are implementing a Zero Trust security strategy, in which no application,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.