Mobility

Solving the Key Challenges in Mobile App Development Lifecycle
In a heavily fragmented mobile environment, developing applications compatible with multiple platforms...

GigaOm Radar for Phishing Prevention and Detection
Get your complimentary copy of this independent GigaOm Research report, which analyzes positioning and...

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...
Enterprise Cloud Solutions
Many traditional infrastructure vendors would have you believe that hyperconverged infrastructure is...

Pure Storage FlashBlade: Unified Fast File and Object (UFFO) Platform
Operational efficiency is the most-cited objective for digital transformation according to ESG research....
Become (and remain) the disruptor
If you thought digital disruption was a one-off process to be completed (or resisted), unlocking a new,...

5G for Dummies
5G, the next iteration of wireless networks, is not merely an incremental increase in network speed and...

3 Reasons the Campus Is the Heart of Enterprise Security
Even as digital acceleration continues to transform businesses, the campus remains the heart of the network....
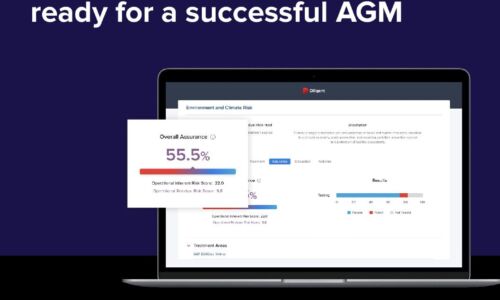
4 tips to ensure your board is ready for a successful AGM
The 2022 AGM season is on course to see unprecedented levels of challenge for boards and businesses....
5 Usage data software options on the market
If you want to offer usage-based pricing to your customers, there are several IT solutions you can choose....

Encryption Is Now a Trojan Horse: Ignore It at Your Peril
The game of leapfrog between hackers and data security professionals continues. No sooner do organizations...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


