Mobile Computing

Adaptive Multi-Factor Authentication
This white paper provides an overview of Okta Adaptive Multi-factor Authentication (MFA). For security...
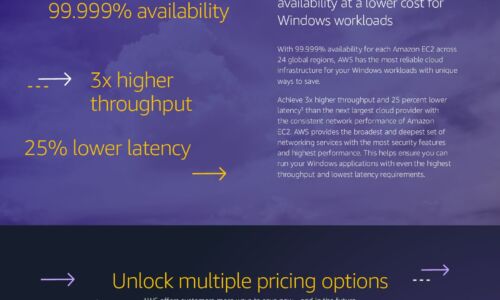
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...

5 Critical Requirements for Internal Firewalling in the Data Center
Preventing hackers from hiding inside large volumes of east-west network traffic has now become critical...

Unified Endpoint Management (UEM): Address 3 Common Challenges
With digital transformation comes mobile devices, apps and high-speed connectivity that make it possible...

Dell And Partners Workforce Productivity Benefits
Dell and its partners provide a range of solutions that enable their customers to transform the capabilities...

Low-Code Guide
Low-Code development is the way to build apps more quickly by reducing the need to code. But that's not...

2019 IT Skills and Salary Report
The 2019 IT Skills and Salary Report provides the most informative and revealing insights into the inner...
The Power Of Personalization
Back in the day, brands' communications to their customers used to consist of a memorable message delivered...
Penetration Testing For Dummies
Target, test, analyze, and report on security vulnerabilities with pen-testing Pen-Testing is necessary...

3 Reasons the Campus Is the Heart of Enterprise Security
Even as digital acceleration continues to transform businesses, the campus remains the heart of the network....
Digital Transformation and Risk for dummies
Digital transformation is a critical priority for many companies across most industries, and it's more...
What your business needs for a hybrid and remote-first workplace
The pandemic redefined 'work' as we know it. Companies adopted new technologies and workflows to support...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
