Internet of Things (IoT)
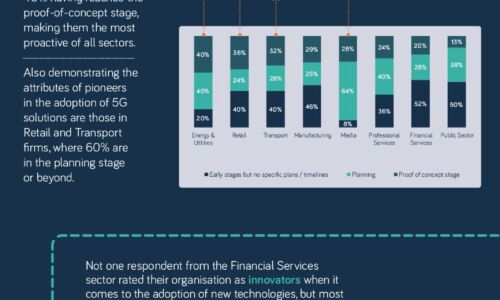
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...

3 technologies you need to future-proof your organization
New technology can be a scary thing. New processes to learn, new systems to teach your team and new ways...

DDoS Threat Landscape Report: DDoS Trends from Q3 2022
DDoS attacks are growing larger, stronger, and more sophisticated. In Q3'22, we observed a resurgence...

How To Choose a Managed Extended Detection and Response Solution
Organizations face major cybersecurity hurdles. The first challenge is finding effective cybersecurity...

The strategic ROI of network management
ROI for all forms of integrated DNS, DHCP and IP Address Management (DDI) solutions is largely comprised...
The Smart Factory
The manufacturing industry is experiencing major disruptions as traditional methods of producing goods...
Reduce Alert Fatigue in Your IT Environment
Security teams are tasked with managing a huge volume of alert logs, and this noise can overwhelm any...

5G Is Changing the Game - Right Now. Is Your Infrastructure Ready?
Advanced 5G use cases will require a fundamental change in infrastructure before they can scale. As network...

The challenges and opportunities for smart cities
With urbanisation continuing at breakneck speed around the world, governments need solutions to make...

Building event-driven architectures with AWS
Key concepts and considerations for building event-driven architectures For organizations that want to...

Redefining Healthcare in the Cloud
Helping you visualise clinical healthcare innovation, and the future of personalised experiences in the...
Reinvention Starts with Cloud Migration of Data Infrastructure
Take the complexity out of your data infrastructure For organizations running legacy data infrastructure...
Unified Fast File and Object (UFFO) Storage
In this book, you get an idea of the vast potential for unstructured data — and also the infrastructure...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
