Hybrid Cloud

Migrating to the Public Cloud: Three Success Stories
Organizations find the public cloud appealing for its promises of agility, reduced costs and developer-friendly...

Top 5 Benefits of VMware Cloud Provider
Explore the unique benefits of partnering with a VMware Cloud Provider Different businesses require different...

Ignite Your Innovation Engine
Dell Technologies believes that the engine you use to drive your business forward should be designed...
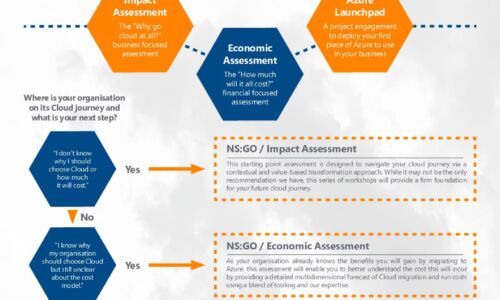
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...
Achieve Cloud Security Cost Savings Through SIEM Optimization
Tame Rising SIEM Costs and Complexity Do you worry that your SIEM is falling behind on efficiently handling...

Powering Digital Transformation with a Hybrid Cloud Strategy
It's not news that companies in every industry are fundamentally transforming the way they do business. Scrappy...

How Cloud Enables Modern Management For Midsize Firms
As midsize firms turn to cloud to enable the agility needed to compete in the future of work, most will...

Enabling Manufacturing Innovation Through the Use of Cloud
In this whitepaper, research firm IDC dives deep into manufacturing use cases in the cloud, evaluates...

A New Paradigm for Salesforce Testing
Just as low-code and no-code development tools are transforming velocity for the new ways that we work,...

Retail eBook
Modern MFA For Retail's Hybrid Workforce Modern retail organizations are moving data to the cloud while...

Four Ransomware Resiliency Challenges You Can Combat with Confidence
Ransomware is a growing thread to operational resiliency in all digital enterprises. These four stories...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


