Data Centers

Understanding the Obstacles to WAN Transformation
Network engineering and operations leaders are looking to software-defined wide area networks (SD-WAN)...
How to Increase Agility with Hybrid Cloud Automation
As organizations innovate faster than ever, they bring new applications and services to market in more...

7 Steps To Get Started with Microsoft Azure
Ready to start using Microsoft® Azure®, but not sure how to get started? Good news: Getting started...

Breaking Down Walls With Digital Technology
The diversity and bureaucratic nature of government agencies have complicated communication for decades....

Multi-cloud Load Balancing for Dummies
Legacy hardware-based load balancers don't meet modern enterprise application delivery requirements in...

The evolution of process automation
Automation has a long and storied history. Today, advancements in artificial intelligence (AI) are spawning...

Economic Impact: Veeam Cloud Data Management
TEI Report: Reduce operating costs of data backup and recovery while reducing data-related risk. ...
The Gorilla Guide to Rapid Restores with Flash and Cloud
Welcome to this Gorilla Guide covering enterprise data protection, backup, and recovery. The purpose...
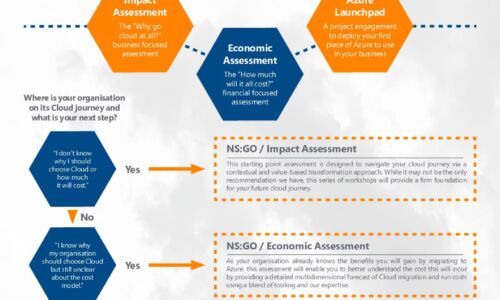
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




