Compliance

Refresh your thinking: You've got a platform problem
The pressure on IT is mounting. Can you meet it before it becomes too great for today's systems and processes?...
Kubernetes on vSphere For Dummies
Discover how building and running containerized applications with Kubernetes on vSphere drives business...
Okta: Decoding Customer IAM (CIAM) vs. IAM
The world of Identity and Access Management (IAM) is rarely controversial. But today, there is a battle...
The 10 Biggest and Boldest Insider Threats of 2019 and 2020
That risk is only increasing in an era of remote working and distributed teams. Without a holistic security...

Forrester: The Total Economic Impact of Dell Technologies Cloud
Dell Technologies commissioned Forrester Consulting to conduct a Total Economic Impact™ (TEI) study...

Pure Unified Fast File and Object Storage
For businesses to maximize the value of their data, they first need to rethink their infrastructure—with...

VMware Multi-Cloud Architecture - Enabling Choice and Flexibility
In today's world, application growth is unprecedented and enterprise applications on a wide range of...
Empowering Medical Manufacturers to Become Leaders
Due to increasing technology and product complexity, regulatory requirements and supply chain issues,...
The Characteristics of Your Future Technology Capabilities
Disruption -- whether big (COVID-19) or small (new start-up competitors) -- has more or less become commonplace...
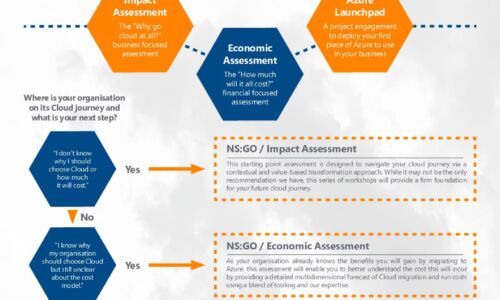
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...
The Ultimate Guide to Workforce Analytics
Learn how Workday can help your organization understand its employee data to make better people decisions...

University of Surrey’s Edification for its Cyber Protection
The University of Surrey is a public research university in Guildford, England, receiving its royal charter...
The Inner Circle Guide to Agent Engagement and Empowerment
Your agents aren't going to ask you for more automated tools, empowered and personalized coaching, and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
